Flawed EVMs or money power, the Election Commission is simply shutting its eyes to solutions

Weeks before the election to the 15th Lok Sabha, the Election Commission of India received a severe jolt when the then Chief Election Commissioner, N Gopalasami, wrote a lengthy missive to the President of India, levelling serious allegations against his colleague and Election Commissioner Navin Chawla and seeking his removal. This was ignored and Navin Chawla was elevated as the CEC in the midst of elections. Three out of the five phases of the election were held under his stewardship and the ruling UPA returned to power.
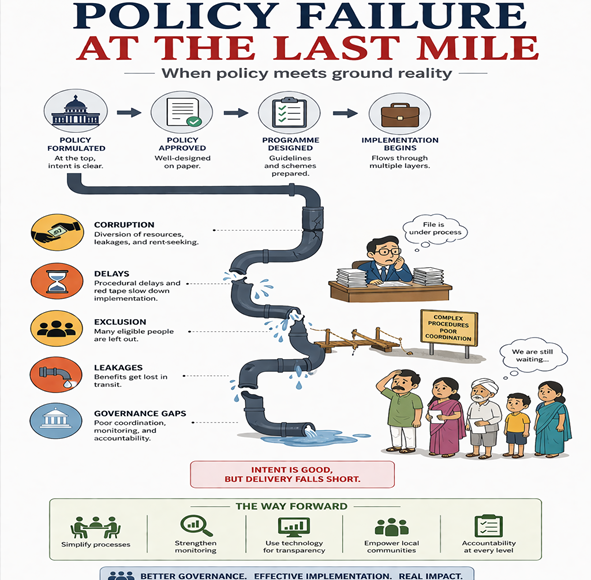
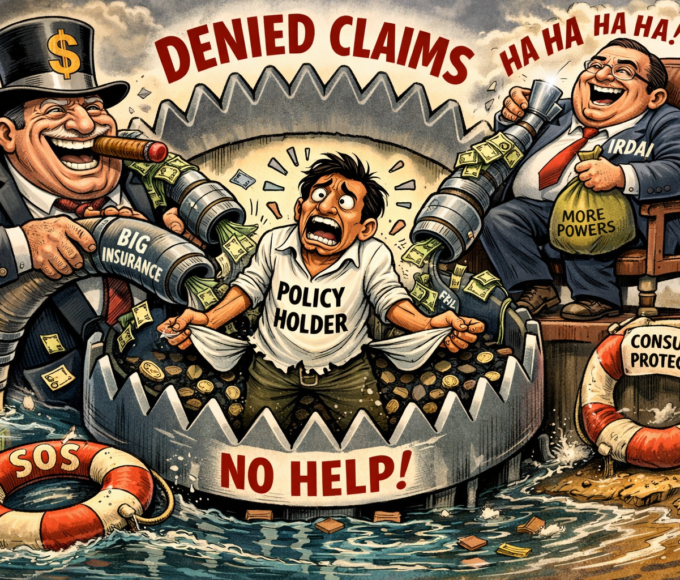
Within days, the Election Commission was flooded with complaints from political parties, NGOs and individuals alleging massive use of money power to purchase votes (up to Rs 70 crore in some constituencies, paid out over several days) and hacking/tampering of the Electronic Voting Machines (EVMs). The EC’s response was ostrich-like regarding money power and evasive regarding EVMs.
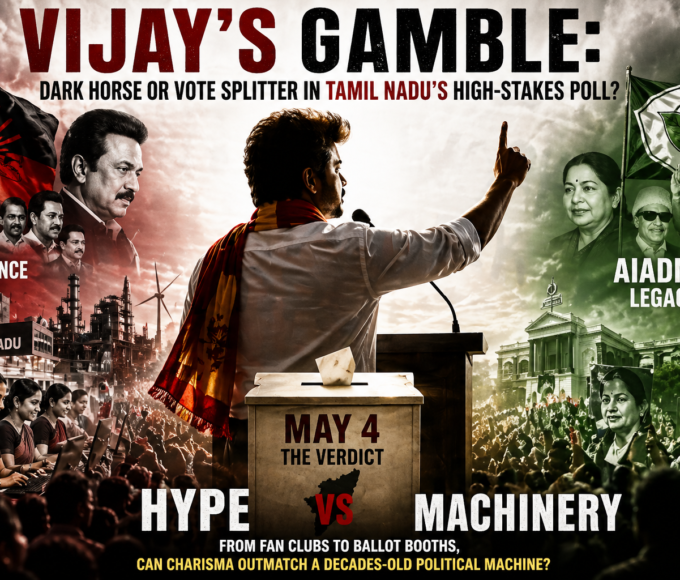
Then followed the open admission to money power by three election bigwigs, past and present – Gopalasami , Election Commissioner SY Quraishi, and Naresh Gupta, long-serving chief electoral officer of Tamil Nadu. Gopalasami set the tone while addressing a select gathering in Chennai: “EVMs cannot be hacked as being alleged because these are stand-alone equipment and not connected to any operating system. We have met party muscle power with state gun power by deploying armed Central police force in polling booths. But we cannot counter money power in a similar manner.”
He conceded that, though EVMs could not be hacked or tampered with, “booth capturing and bogus voting is very much possible and very much prevalent”. The statements of Quraishi and Gupta were on the same lines, thus creating a credibility crisis about the EC and the electoral process.
Next came the Supreme Court direction to election watchdog NGO Jan Chaitanya Vedika to approach the Election Commission in the matter of integrity of the electronic voting system. Three High Courts – Madras, Bombay and Madhya Pradesh – also issued similar directives to parties who approached them.
The EC hurriedly summoned the complainants to demonstrate the “tamperability” of EVMs on its premises between August 3 and 8 with a caveat: “Commission is sure of its non-tamperability. EVMs are fully tamper-proof”. This amply evidenced a closed mindset.
Though not all parties appeared, the EC went ahead. A hundred EVM samples, obtained on random basis from various states, were kept at the Commission’s office in the presence of a “technical experts group” as well as engineers representing the EVM manufacturers – BEL and ECIL.
Brushing aside objections from political parties and individuals, the EC foreclosed the issue with a press statement on August 8: “The Election Commission would like to underline that it always had a firm conviction and complete satisfaction that EVMs could not be tampered with….What has been demonstrated or claimed to have been demonstrated is on a privately assembled lookalike of ECI-EVMs and not the actual ECI-EVM …. Today, the Commission once again completely reaffirms its faith in the infallibility of the EVMs. These are fully tamper-proof, as ever.”
Nevertheless, in subsequent presentations by the NGO and representation from some parties and individuals, the “infallibility” of the EVMs was shown up (see box).
Under the paper ballot system, the EC had total control over all stages of the electoral process. Election agents had the facility of looking inside ballot boxes. Voters had the satisfaction of checking the accuracy of the ballot paper before marking it and verifying whether he/she had correctly marked it. Reconstruction of the vote for authentication in case of electoral dispute was possible.
Under the electronic voting system, the EC seems to have lost control over vital stages of the electoral process. External agencies undertaking the critical tasks as described above could be replete with mischief and manipulation, raising all kinds of suspicion about the integrity of the electoral process. Neither the election agents nor the voters have the facility and satisfaction of scrutinizing the ballot boxes and ballot papers prior to and during the casting of the vote. And there is no physical reconstruction of the vote in case of dispute.
The oft-stated idiom that Caesar’s wife must be above suspicion applies to the EC and the burden of proving the integrity of the electronic voting system in an open and transparent manner rests squarely with the Commission
Having realized the seriousness of the issues involved, the EC has relented and agreed to look at the matter afresh with an open mind. This is a welcome step, for this is the first time in independent India that the electoral process and election mechanism have come under such strong suspicion and challenge. The oft-stated idiom that Caesar’s wife must be above suspicion applies to the EC and the burden of proving the integrity of the electronic voting system in an open and transparent manner rests squarely with the Commission.
The EC would do well to set up a committee of independent experts comprising EC and party nominees, to go into the issue of tamperability of EVMs and the entire electronic system of polling in great detail. To facilitate organized and transparent functioning of the committee, the EC should draft appropriate guidelines in consultation with parties. This is the least the EC should do to douse the flames of suspicion that could spread like wildfire.
It may be true that party money power cannot be physically countered by state money power. But by creating fear in the minds of the corrupters, the EC can certainly fight it
Equally serious is the devastation caused by money power. It may be true that party money power cannot be physically countered by state money power. But by creating fear in the minds of the corrupters, the EC can certainly fight it. It is difficult to believe that, with the vast contingent of observers with video and still cameras deployed by the Commission, it does not get actionable evidence of such largescale bribery, which even the common man knows about. Why then is the EC passive and inactive?
Why can’t the EC countermand elections in constituencies where massive money power is being deployed, as described in Section 123 of the Representation of the People Act? It would send shivers down the spine of the cash-and-carry candidates who are destroying the credibility of the electoral process. Is it the failure of the EC or the much celebrated band of observers who do not seem to be doing anything worthwhile except enjoying an outing at taxpayer’s expense?
As of now, provision for countermanding under Section 59 A 2(b) of the Act is available for booth capturing which covers the physical act of taking possession of polling stations, ballot boxes/EVMs or ballot papers because of which the result of the election is likely to be affected. Since proven pre-poll vote purchase would also have the same result, there is nothing wrong in invoking this strong psychological weapon to make the elections free and fair. If need be, the Act could be suitably amended without delay.
‘Tamper-proof’ EVMs – A falsity
- ECIL- and BEL-manufactured EVMs use 8-Bit Chip. Software – also developed by these companies – is sent to factories in Japan and the US for fusing the code into the chip. The process of sending the code is non-transparent and there is every possibility for swapping of the code and insertion of a Trojan, which can be subsequently activated to manipulate the machine.
- As yet there is no mechanism or method to verify whether the chip used in the voting machines contains the original code or not. After the chips are fused with the software code, they are shipped back to ECIL or BEL, who then plant them into the EVMs they make. There is no certainty as to the origin, reliability, security and integrity of the agencies handling the software and the chips.
- These chips can also be procured from the same manufacturer with the original code along with the Trojan in it through the distributor or his agent or some other means. These chips with the manipulated code can be delivered to the manufacturer of EVMs as if they are original chips.
- After the fusion of software, the chips are masked. There is no way masked chips can be read, even by the manufacturer. So it is not possible for BEL/ECIL to check them except through a functionality test.
- A functionality test cannot in any way find out if a Trojan has been introduced, maliciously or otherwise, in the software by the company that masked the chips. The Election Commission never checked the software of the machines.
- All these flaws and deficiencies make switching of votes during polls or hacking/manipulating the results a distinct possibility.
IAS (retd) with a distinguished career of 40 years - worked in Army, Govt, Private, Politics & NGOs.